Pente HyperCore: Private 5G & Cloud Mobile Core. Radically Simplified.
Cloud-native, SaaS-based mobile core and orchestration designed for seamless IT integration and unparalleled flexibility across Private Networks, MNO/MVNO cores, and EVNO solutions.
Why Choose Pente HyperCore?
Our platform transforms how enterprises and operators deploy and manage mobile networks.
IT-Centric Simplicity
Manage cellular networks like IT infrastructure with our intuitive portal and comprehensive API suite for seamless integration.
Rapid Deployment
Transform your network infrastructure in minutes with our plug-and-play core and intelligent orchestration system.
Converged Core (2G-5G SA)
Future-proof your network with our comprehensive platform supporting all generations of cellular technology.
Unmatched Flexibility
Deploy anywhere with our cloud, edge, or hybrid solutions. Maintain vendor independence with our RAN-agnostic approach.
Robust Security
Protect your network with our comprehensive zero-trust security framework, built from the ground up for enterprise needs.
Proven Scalability
Scale with confidence using our platform trusted by global operators and enterprises to manage millions of connections.
Connectivity Solutions for Every Need
Flexible, powerful options for enterprises and operators.

Private 5G/LTE Networks
Build and manage secure, high-performance private cellular networks with enterprise-grade control. Perfect for Industry 4.0, smart venues, and mission-critical communications.
Explore Private 5G/LTE Networks
MNO/MVNO Core
Transform your mobile core with our cloud-native, scalable solution. Support all generations from 2G to 5G SA/NSA with unprecedented operational efficiency.
Explore MNO/MVNO Core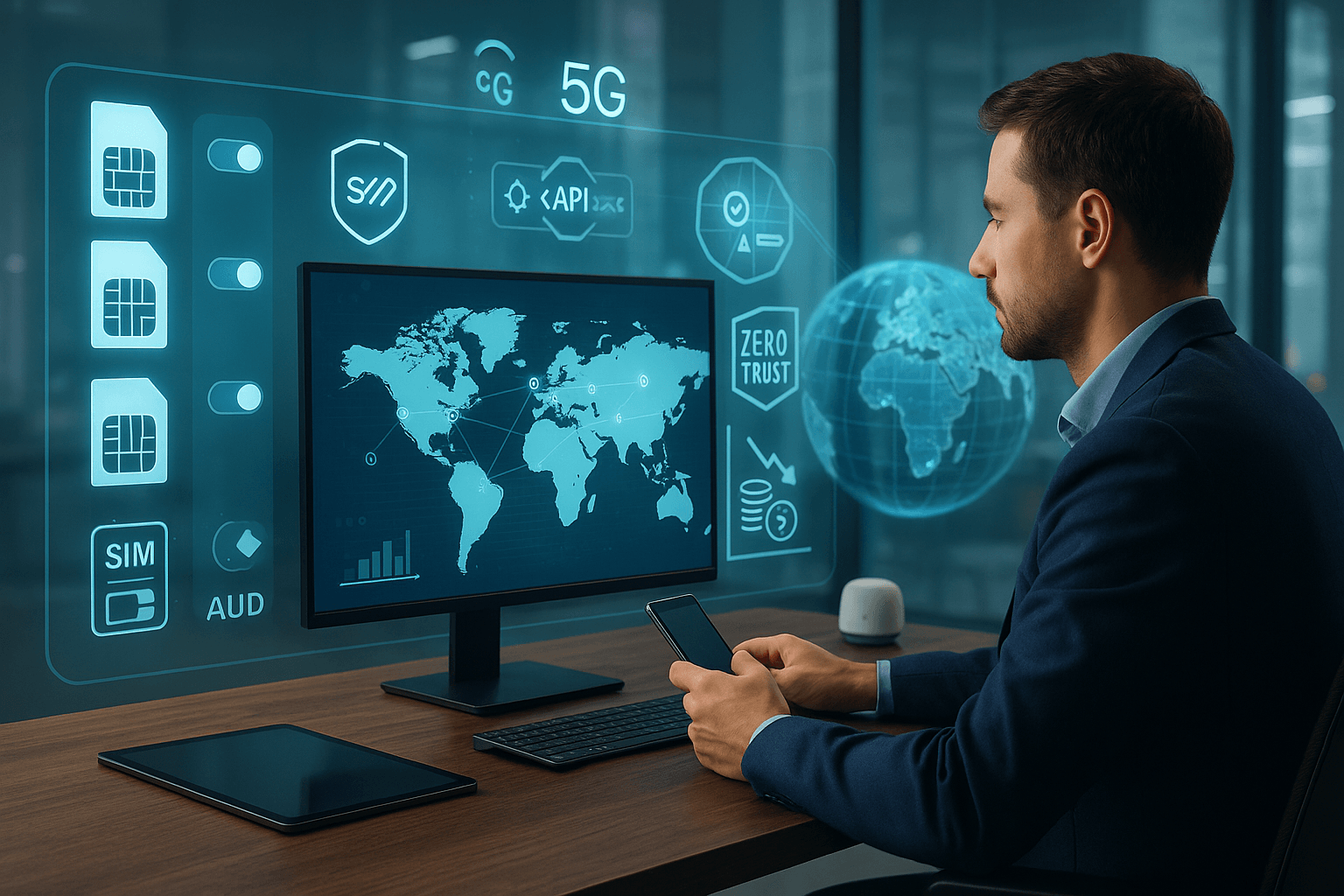
EVNO Suite
Take control of your global connectivity with our Enterprise Virtual Network Operator solution. Manage costs, security, and quality across multiple carriers worldwide.
Explore EVNO Suite
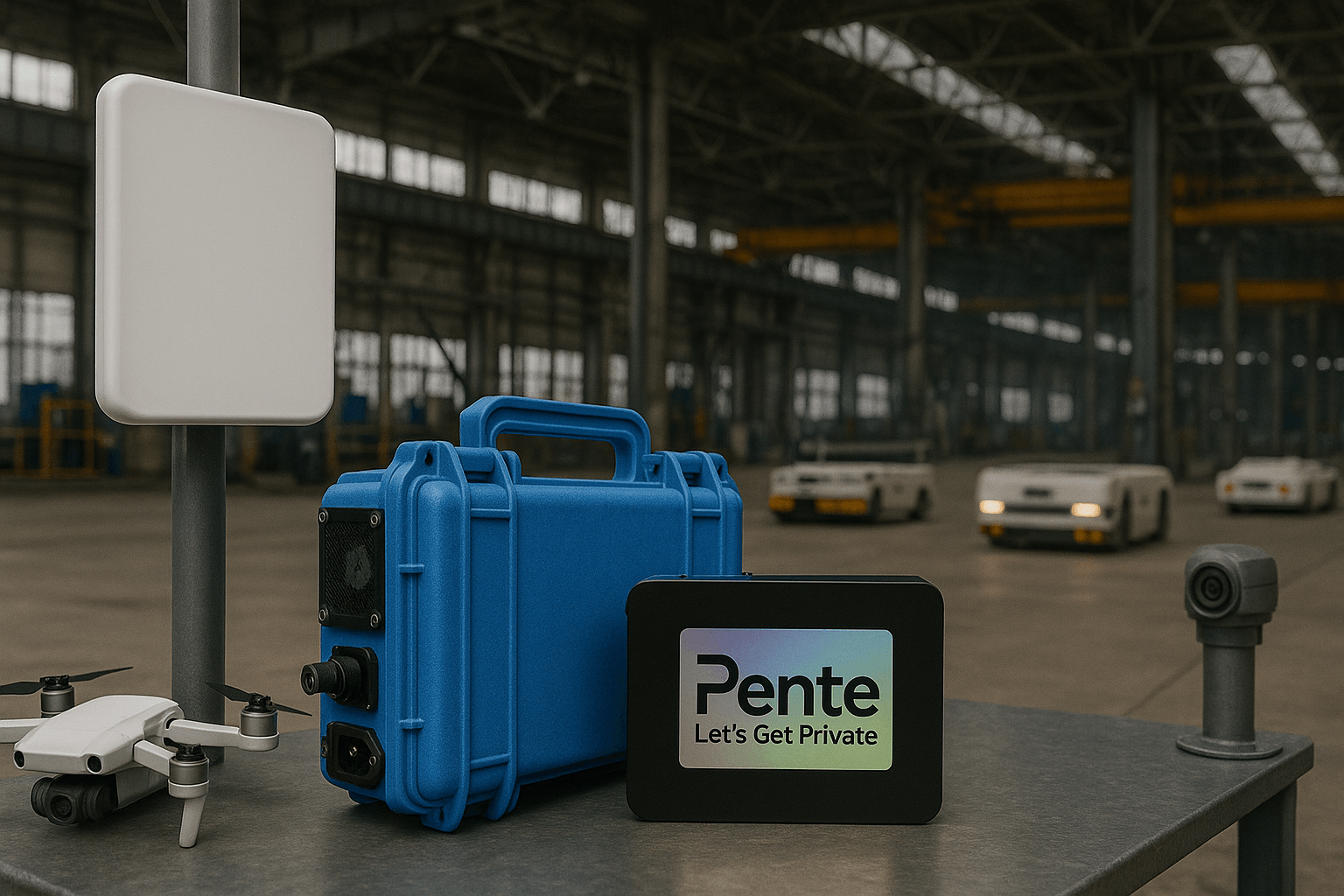
Network-in-Box
Deploy a complete, pre-configured private LTE/5G network in hours. Everything you need for instant private wireless connectivity in one package.
Explore Network-in-BoxMeet the HyperCore Platform
A comprehensive solution for deploying, managing, and scaling cellular networks with unprecedented ease.
Cloud Control Center
Intuitive management portal with orchestration capabilities, real-time analytics, and 1000+ APIs for seamless integration.
Learn more about Cloud Control CenterSurvivable Edge
Local compute solutions for low-latency, high-reliability operations, even when cloud connectivity is lost.
Discover HyperCore Edge Solutions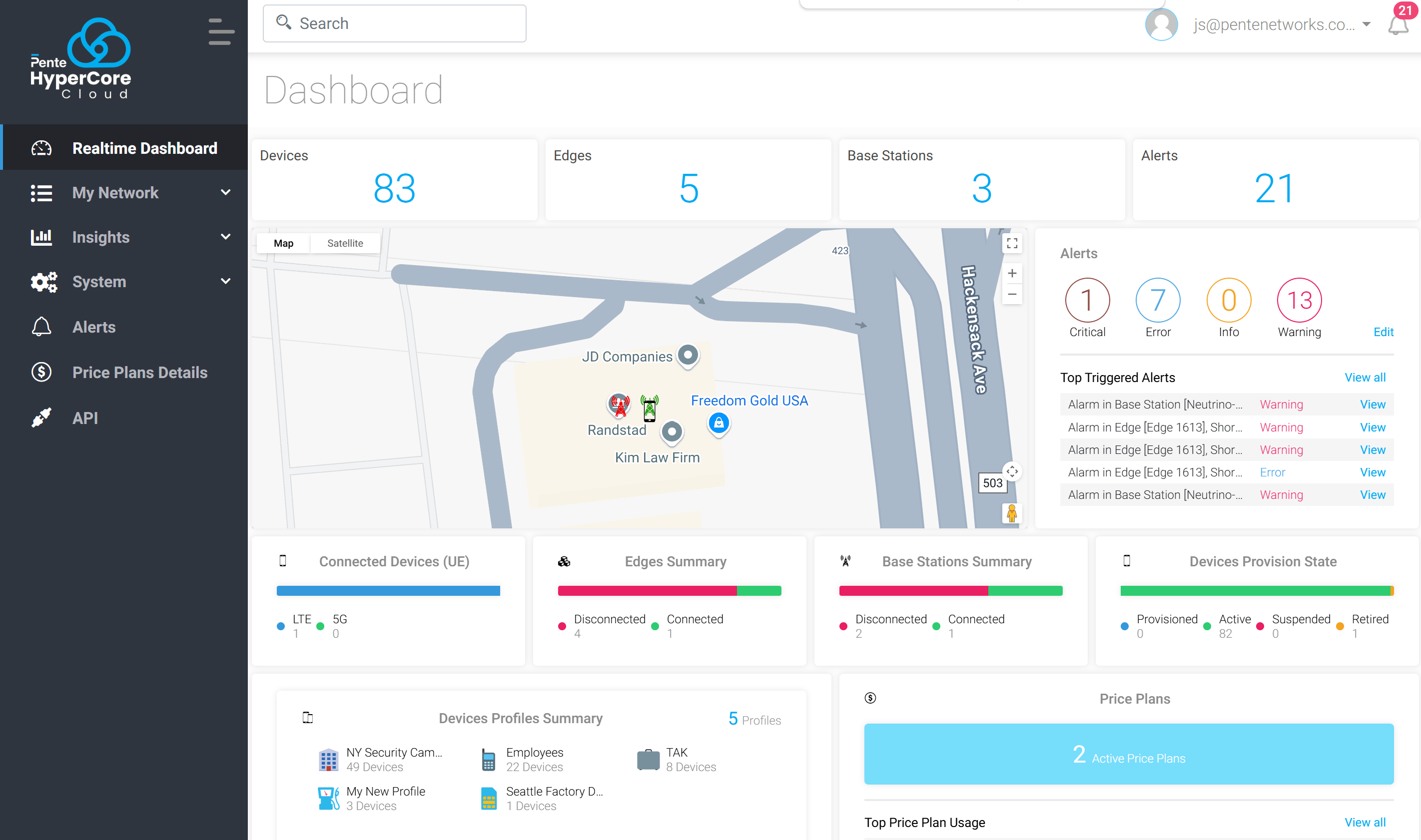
HyperCore by the Numbers
Our platform delivers enterprise-grade performance and reliability at scale
Our Partners & Customers




































Ready to Transform Your Connectivity?
Discuss your requirements with our experts and see HyperCore in action.